From Continuous Training Strategy to a Practical Implementation Illustrated with M&NTIS Platform and Sekoia SOC Platform
When a real cyber incident occurs, success rarely depends on a single analyst or a single alert. It depends on how well a team can collectively understand a situation, coordinate investigations, make decisions under uncertainty, and prioritize response actions while the attack is still unfolding.
For SOC and CERT teams, operational confidence is built through practice; not only technical practice, but team-based rehearsal under realistic conditions. This is the purpose of regular Live Fire Exercises.
This article first explains why continuous, team-oriented Live Fire training is essential for SOC and CERT readiness. It then demonstrates how such exercises can be implemented in practice using M&NTIS Platform, with a specific focus on its integration with Sekoia SOC Platform.

1. Why regular Live Fire Exercises are essential for SOC/CERT team readiness
From individual skills to collective performance
Most SOC and CERT analysts are technically proficient. They understand detection logic, attacker techniques, and investigation workflows. However, real incidents rarely fail because of a lack of knowledge; they fail due to misalignment, delayed decisions, or poor coordination.
Live Fire Exercises are designed to train:
- How analysts collaborate during investigations
- How context is shared across roles and seniority
levels
- How escalation decisions are made
- How response actions are discussed, prioritized, and justified
The goal is not to test individuals in isolation, but to rehearse how the team operates as a unit.
2. Implementing team-based Live Fire Exercises with M&NTIS Platform
Focus on the Sekoia SOC Platform integration
M&NTIS Platform is a SaaS B2B Cyber Range designed to reproduce realistic attack scenarios in a controlled environment. These scenarios, provided through a curated catalog, emulate adversary behavior across complete kill chains, generating telemetry similar to what a production SOC would see.
From a Blue Team perspective, M&NTIS Platform provides:
- A safe and isolated environment for running complex scenarios.
- A catalog of pre-built scenarios mapped to frameworks like MITRE ATT&CK.
- Native integration with detection and response tools, including Sekoia SOC Platform.
M&NTIS Platform integrates with multiple external SIEM solutions, allowing organizations to conduct Live Fire training using their existing detection and investigation stack they use every day. In this article, we focus on the integration with the Sekoia SOC Platform as an illustrative example.
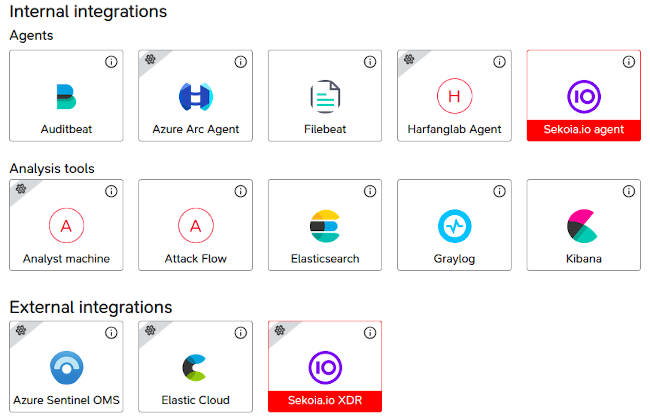
M&NTIS automatic integration with Sekoia SOC Platform
The user can select Sekoia agent and Sekoia XDR (SOC Platform) to ensure complete usage of M&NTIS’ integration with Sekoia.
During M&NTIS lab launch, Sekoia agents thus gets automatically deployed on simulated endpoints and systems, and an new dedicated entity is created on Sekoia SOC Platform.
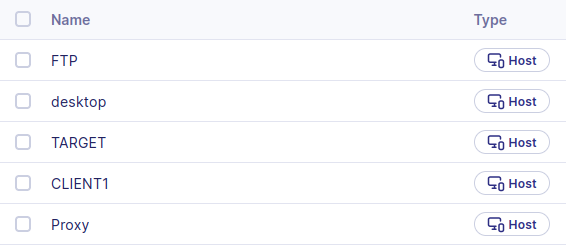
Sekoia SOC Platform visibility on M&NTIS lab events
Once Sekoia agents are enrolled, Sekoia SOC Platform gets M&NTIS lab assets visibility.
Then, the following capabilities are processed:
- Sekoia agents collect endpoint telemetry (processes, file operations, registry, network), just as it would be in a production environment.
- Existing detection content, dashboards, and playbooks can be leveraged during training.
3. Alert-driven investigation as a coordinated team effort
Phase 1: Collective qualification of the incident
As the first alert is triggered in Sekoia SOC Platform, the team must rapidly align on a shared understanding of the situation.
Role focus: SOC L1 Analyst
Primary responsibility: Alert triage and initial qualification
- Validate alert context and severity
- Identify impacted user, host, and timeframe
- Decide whether escalation is required
Training value:
Live Fire Exercises expose L1 analysts to ambiguous alerts in
noisy environments, helping them build confidence in
escalation decisions rather than relying solely on rigid
thresholds.
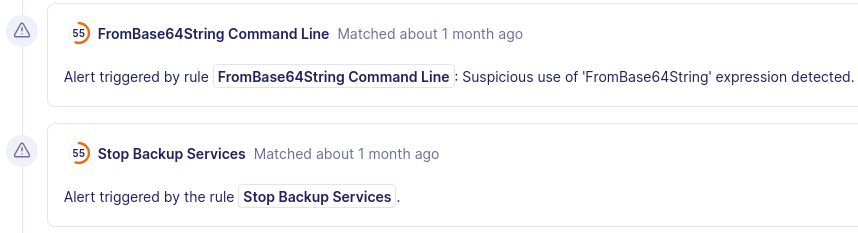
Training in the noise of a live attack
In addition to malicious actions, M&NTIS Platform simulates legitimate business activity:
- Normal user logons and logoffs.
- Routine file access and application use.
- Regular network communications.
This creates signal-to-noise conditions very close to real environments, forcing analysts to distinguish malicious activity from benign noise; a key skill for any SOC or CERT.
AI-Powered case creation with Sekoia SOC Platform
One of the standout features of Sekoia SOC Platform is its ability to automatically generate investigation cases using AI, giving analysts immediate context and guidance.
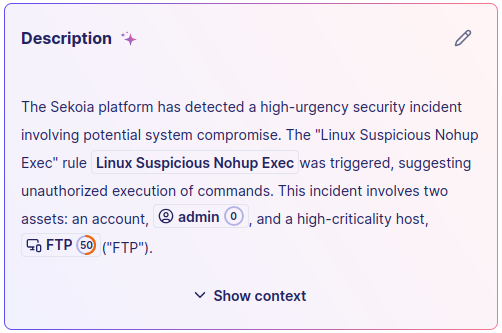
Sekoia not only creates the case automatically but also explains why it was generated, helping analysts understand the threat, prioritize response, and take action faster. This feature allows SOC teams to train and operate efficiently, even in environments with high noise, by focusing directly on actionable threats.
Phase 2: Distributed investigation and hypothesis building
Once the incident is confirmed, the investigation becomes parallel and collaborative.
Role focus: SOC L2 Analyst
Primary responsibility: Deep investigation and correlation
- Reconstruct process execution timelines
- Analyze authentication anomalies and lateral
movement
- Correlate endpoint, directory, and network signals
Training value:
The exercise reinforces structured investigation methodologies
and hypothesis-driven analysis, while forcing L2 analysts to
continuously share findings with the rest of the team.
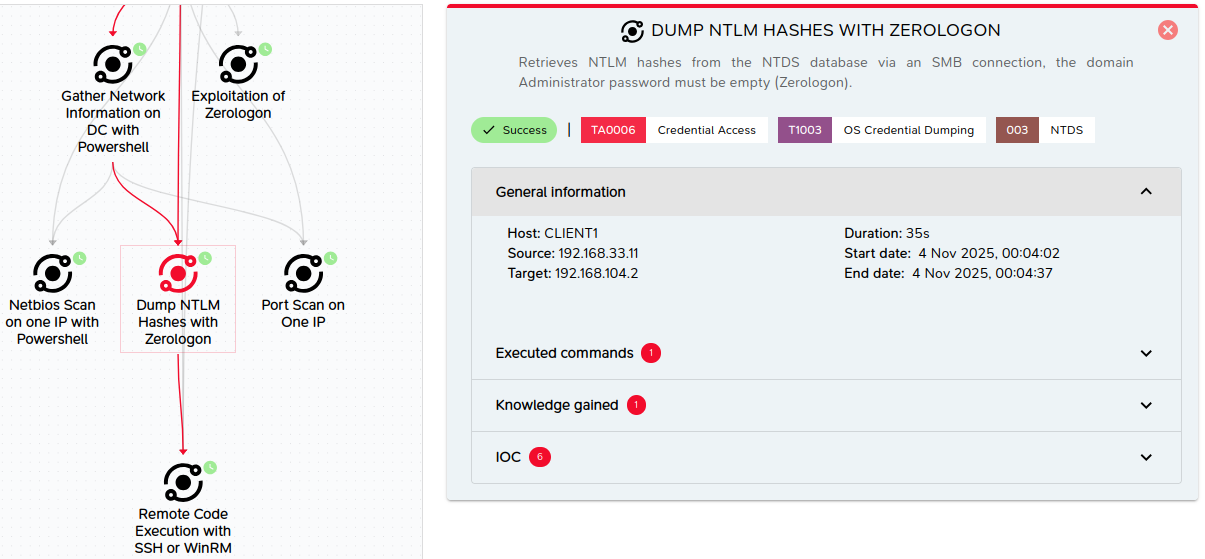
Automated, live Adversary emulation with M&NTIS
M&NTIS Platform runs realistic attack simulations automatically, in real-time, reproducing genuine threat behavior and evolving adversary techniques. This includes:
- Full attack chains (initial access, persistence, privilege escalation, lateral movement, exfiltration).
- Dynamic behavior that generates varied telemetry over time.
- Alignment with known attacker TTPs.
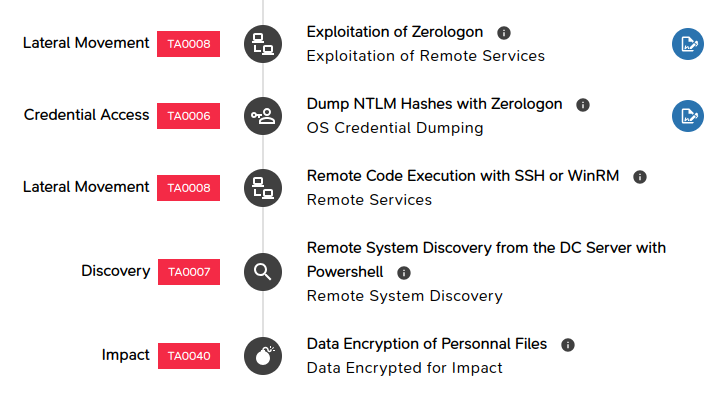
Correlated alerts to guide analysts’ investigations
The Sekoia SOC Platform helps analysts make sense of complex environments by correlating multiple alerts into a single investigation case. This correlation highlights relationships between events and suggests potential attack paths, giving analysts insights to progress in their investigation.
4. Escalation, leadership, and operational decision-making
As evidence accumulates, for example, signs of lateral movement or privilege escalation, the exercise shifts toward incident coordination and leadership.
Role focus: Incident Lead / CERT Analyst
Primary responsibility: Coordination and decision-making
- Maintain a global view of the incident
- Validate analyst conclusions and priorities
- Decide when and how to escalate internally
- Coordinate response actions
Training value:
Live Fire Exercises help incident leads practice
decision-making under uncertainty, balancing investigation
depth with containment urgency.
5. Countermeasures and prioritization under real constraints
At multiple points during the scenario, the team must discuss and prioritize response actions:
- Assign response actions (e.g. quarantine host, disable user account, block IP address)
- Continue monitoring to gather intelligence
- Track remediation steps with status updates and ownership
- Document evidence and decisions for audit and post-incident review
- Coordinate across teams (SOC, IT, CERT) within a single workflow
These decisions are deliberately not scripted. The exercise does not enforce a single “correct” response, but exposes the operational and investigative trade-offs of each option.
6. Management perspective and strategic alignment
Live Fire Exercises are not limited to technical validation; they also provide visibility into team maturity and organizational readiness.
Role focus: SOC / CERT Manager
Primary responsibility: Oversight and strategic assessment
- Observe coordination and escalation efficiency
- Identify bottlenecks in processes or tooling
- Assess confidence and autonomy of the team
- Prioritize improvements based on observed gaps
Training value:
Managers gain concrete insights into how their teams operate
under pressure, enabling data-driven decisions on detection
tuning, staffing, and process evolution.
7. Post-exercise debrief and continuous improvement
Each Live Fire Exercise concludes with a structured, team-wide debrief:
- What signals were detected early or missed?
- Where did coordination slow down?
- Which decisions created uncertainty or friction?
- What should change in detection logic, playbooks, or communication paths?
These lessons learned can feed into a structured training roadmap, using M&NTIS scenario catalog to reinforce specific capabilities over time. Indeed, because scenarios are automated and repeatable via M&NTIS Platform, teams can replay the same scenario or run similar scenarios after improvements and measure progress over time.
Using attack path explainability for debrief
Thanks to the attack path explainability feature in M&NTIS Platform, the exact sequence of attacker actions and their metadata can be used during the debrief. Teams can thus:
- Compare their investigation timeline with the real attack path.
- Identify which signals were available at each stage in Sekoia SOC Platform.
- Discuss missed opportunities for earlier detection or containment.
This makes debrief sessions concrete and constructive.
Conclusion: Training people and teams, not just tools
Live Fire Exercises reach their full value when they go beyond technical detection and focus on coordination, communication, and decision-making.
For SOC and CERT teams using Sekoia SOC Platform today, M&NTIS Platform offers a powerful and realistic environment to train and upskill analysts:
- Juniors can learn investigation practices and procedures directly in Sekoia SOC Platform, on realistic attacks and noise conditions.
- Confirmed analysts can be regularly challenged with complex adversary behaviors and multi‑phase scenarios.
- Teams can rehearse collaboration, communication, and escalation workflows under realistic constraints.
By combining realistic attack simulation through M&NTIS Platform with SIEM-driven investigation, such as with Sekoia SOC Platform, organizations can embed team-based Live Fire training into their SOC and CERT operations; increasing confidence, readiness, and resilience before the next real cyber incident. Besides, organizations can rely on recurring planned exercices to transform occasional training into a structured and continuous capability‑building program to strengthen their Blue Team.