April 2, 2025
Unlocking Access to Attack Datasets
We’re excited to announce that M&NTIS Platform is now available in a Free version, giving users the opportunity to access valuable attack datasets. These datasets include network traces (PCAP) and system logs, captured during the execution of various attack techniques and scenarios. This is a huge step forward for anyone looking to test and enhance their cybersecurity capabilities, through reproducible means.
These datasets have been produced by executing a attack techniques and scenarios targeting a simulated information system. This information system runs inside a Cyber Range isolated environment, in order to provide realistic network and log traces.
Dataset use cases
Whether you are testing your own cybersecurity solutions, developing new tools, or conducting academic research, these traces will help you build a deeper understanding of the tactics, techniques, and procedures (TTPs) used by attackers. The ability to analyze PCAP and log files from actual attack simulations provides valuable data to improve defensive strategies and better prepare for emerging threats.
Multiple use cases are covered by having access to those datasets:
- Security Testing & Validation: If you are evaluating security solutions, these datasets can be used to test how well your defenses handle real-world attack patterns.
- Training & Skill Development: Security professionals and students can use the datasets to improve their skills by analyzing attack behaviors.
- Research & Development: Researchers can use the data to analyze traces from attack vectors and improve detection mechanisms.
Viewing datasets
In the M&NTIS Plaform web app, the dataset list is accessible on the left menu:
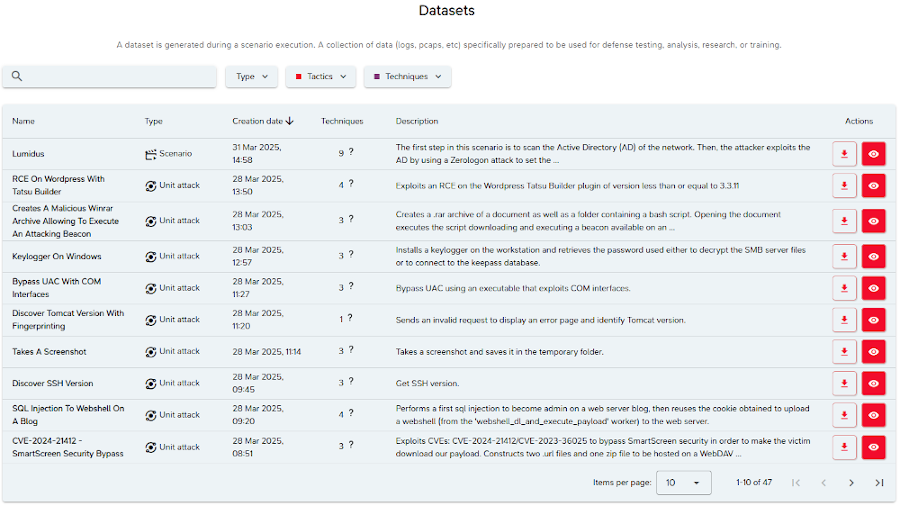
Datasets can be filtered according to their type (e.g. datasets from unitary attack action or from complete scenario). Once inside a dataset, the user can access several tabs to visualize the data:
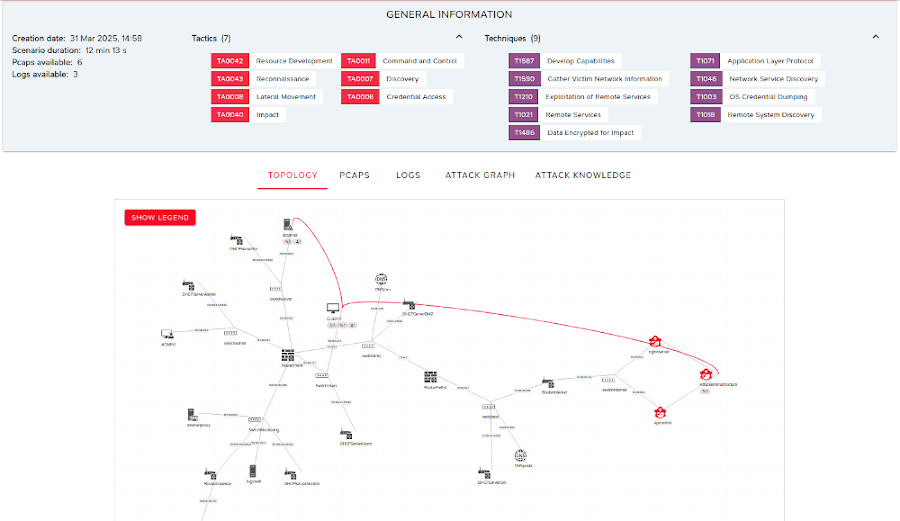
The following tabs are currently available:
- Topology: the emulated IT system topology containing the attack infrastructure.
- PCAPS: network traces, collected on each switch of the topology.
- Logs: system and applicative logs retrieved from Linux and Windows endpoints.
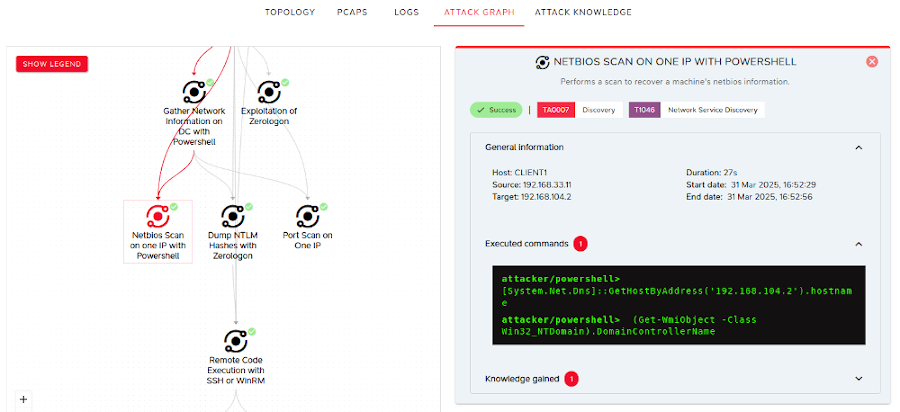
- Attack graph: explainability of the attack steps performed by the M&NTIS Adversary Emulation engine.
- Attack knowledge: knowledge gained from the targeted IT system after each attack step.
The attack graph tab provides detailed metadata for each attack step of the scenario:
Dataset structure
You can download either the whole dataset or subparts of the datasets (e.g. only specific PCAP or log files).
A dataset is provided as ZIP archive composed of the following elements:
./manifest.json file: a JSON document with general information about this dataset and its resources (description, creation date, used attack tactics and techniques, resource list, …)../topology.yaml: a YAML document describing the network topology of the simulated information system../assets/ folder: a list of JSON documents containing information regarding the information system assets../pcaps/ folder: PCAP files containing the network activity captured from specific probe positions../logs/ folder: event log files for each node (computers and servers) on the network topology, captured with tools like nxlog, auditbeat, winlogbeat, sysmon, etc../redteam_reports/ folder: several JSON documents containing:attacks.jsonfile: an attack report with metadata detailing each attack step (timestamps of actions, targeted node(s), relay node(s), attack command(s), …)sessions.jsonfile: the list of attack sessions (C&C) and their metadatas (compromised host IP, user account, level of privileges, …).knowledge.jsonfile: a database containing information collected by the attacker regarding the targeted information system.infras.jsonfile: the list of ‘internet’ attack nodes created by the attacker to perform several attack steps, and representing the attacker infrastructure (C&C server, exfiltration server, staging server, …).
Get Started Today
To get started with the Free version of M&NTIS Platform, simply sign up on our App and start exploring the datasets:
==> https://app.mantis-platform.io <==
These datasets can be used inside your organization (e.g. for training or assessing you defense performance), or for academic purpose. If you want to use M&NTIS datasets for commercial purpose, please contact our sales team.

