Cybersecurity exercises are increasingly recognized as a cornerstone of modern defense strategies. Organizations use simulations, training, and crisis scenarios to improve their readiness.
Yet, “cyber exercise” is still often used as a catch-all term—covering very different formats with radically different objectives. The result is a common frustration: well-executed exercises that do not always test what they were supposed to.
This article proposes a structured overview of the main types of cybersecurity exercises—what they are good for, their caveats, and how to integrate them into a coherent, data-driven strategy.
A Capability-Driven View of Cyber Exercises
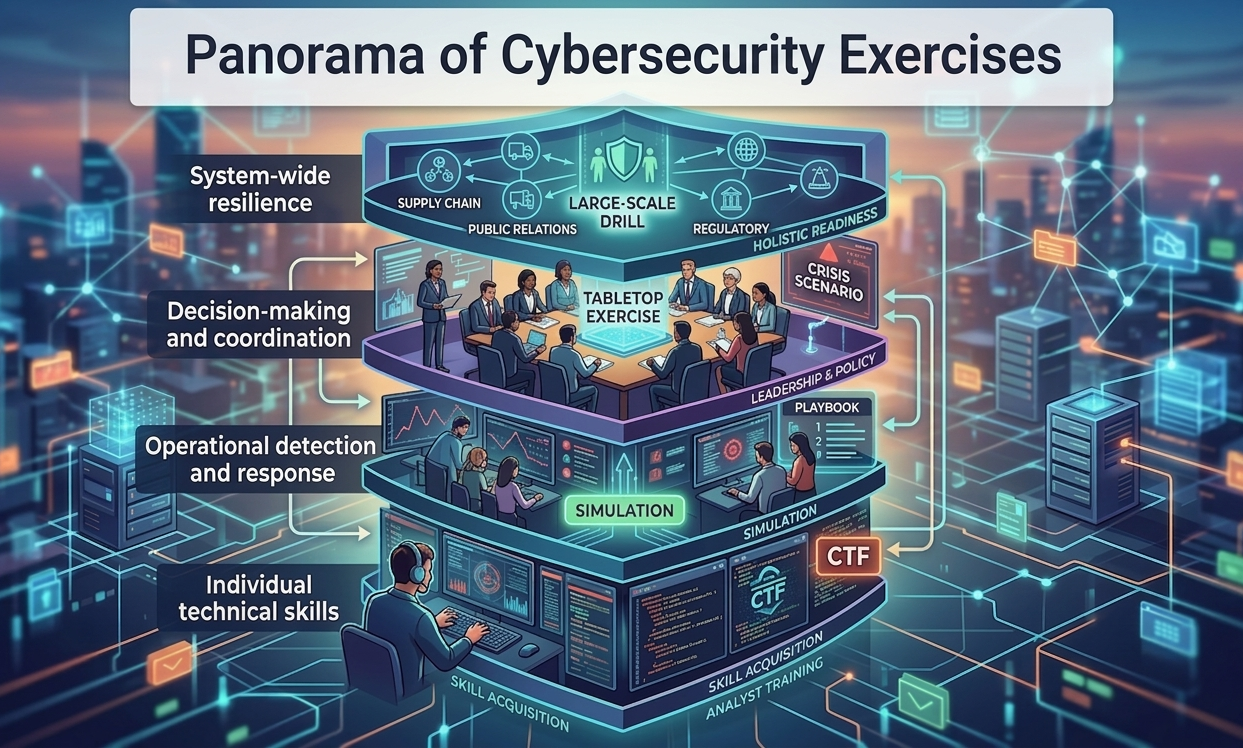
Rather than classifying exercises by format or technical tool, it is more useful to look at what capability they are designed to develop or validate. Every exercise targets one or several layers of organizational resilience:
- Individual technical skills: Can an analyst perform the task?
- Operational detection and response: Do our tools and playbooks work together?
- Decision-making and coordination: Can we lead through a crisis?
- System-wide resilience: How does the whole organization survive a major blow?
Each type of exercise below addresses specific layers—but none covers them all.
1. Skills-Based Exercises (CTFs & DFIR Labs)
These formats form the foundation of Blue Team Training, building the individual technical competencies required for SOC and incident response roles. Defensive CTFs focus on blue-team skills through gamified challenges, emphasizing forensic analysis, log investigation, and artifact collection in a controlled environment. DFIR Labs (Digital Forensics and Incident Response) provide structured, scenario-based training where analysts perform memory forensics, conduct log analysis, and reconstruct attack timelines. Both formats build hands-on defensive skills without risking production systems, allowing analysts to practice against known attack patterns and develop muscle memory for investigation workflows.
When to Use Each
- CTFs: Regular practice sessions, team competitions, and maintaining proficiency through gamification
- DFIR Labs: Deep-dive training, certification preparation (GCFA, GNFA, BTL1), and learning forensic methodologies
Caveats
- Isolated challenges: Both often lack the “background noise” of a real network environment.
- Linearity: Scenarios may not reflect real investigations where data is incomplete or overwhelming.
- No coordination: They test the “individual contributor” rather than team dynamics.
How to Use Them Effectively
Use defensive CTFs and DFIR labs as a continuous skill-building foundation:
- Onboarding and upskilling: Provide structured learning paths for new analysts and emerging threats
- Certification preparation: Support exam readiness for credentials like GCFA, GNFA, BTL1
- Maintaining proficiency: Enable regular, gamified practice to keep skills sharp
These individual-focused exercises strengthen technical foundations that are then mobilized in more complex, team-based simulation contexts.
2. Discussion-Based Exercises (Tabletop)
Traditional tabletop exercises focus on “paper-based” reality: roles, responsibilities, decision-making processes, and communication flows. Participants walk through hypothetical incidents step-by-step, answering questions like “who decides?” and “what authority do we have?” These exercises align senior stakeholders on crisis governance, structure crisis cells with clear roles, and identify gaps in playbooks before they matter.
When to Use Them
- Annually: Refresh crisis procedures and contact lists
- After organizational changes: When key personnel, roles, or business priorities shift
- Following real incidents: Update playbooks based on lessons learned
Caveats
- Lack of friction: There is no real-time pressure or technical hurdle to test decision quality.
- The “Ideal Case” bias: Participants describe how they expect to behave, not how they will under stress.
- No validation: You validate the plan on paper, not the execution in practice.
How to Use Them Effectively
Use tabletop exercises as the foundation for crisis governance:
- Building crisis playbooks: Gather input from all stakeholder groups (Legal, PR, HR, Executive)
- Testing escalation matrices: Ensure everyone knows when and how to escalate
- Identifying authority gaps: Find where decisions get stuck due to unclear decision rights
These discussion-based exercises are the prerequisite for any mature crisis cell and should precede more intense formats like dynamic tabletops or live simulations.
3. Dynamic Tabletop Exercises (Inject-Based)
Dynamic tabletops extend the traditional format by introducing real-time stimuli (“injects”) that simulate a deteriorating situation. Unlike static tabletops where the scenario is discussed linearly, injects arrive unpredictably via phone calls, simulated emails, social media alerts, news feeds, or regulatory notifications.
They bring a necessary layer of realism by introducing cognitive load and time pressure, revealing communication gaps and forcing participants to react to a shifting landscape.
- Testing communication protocols under stress and information overload
- Practicing decision-making with incomplete information
- Building resilience to external pressure from media, customers, and regulators
- Validating escalation timing and crisis communication skills
When to Use Them
- Quarterly: As a step up from static tabletops for teams with established crisis playbooks
- Before hybrid exercises: To prepare crisis teams for the “fog of war”
- For role-specific training: Focused sessions for PR teams, legal advisors, or executives
Caveats
- Technical disconnect: No validation of actual technical detection or response capabilities
- Script dependency and artificiality: Poorly timed injects can feel “railroaded,” and participants still know it’s not real, which affects behavior
- Facilitator expertise: Requires skilled facilitators who can adapt injects in real-time
How to Use Them Effectively
Dynamic tabletops act as a bridge between pure governance and technical operations:
- Testing communication cadence (hourly updates, executive briefings, customer notifications)
- Practicing information validation before making public statements or executive decisions
- Building muscle memory for incident command structures and decision authorization
Use them when teams have mastered static tabletops but aren’t ready for the complexity and cost of full technical simulations.
4. Technical / Operational Exercises (Simulations & Cyber Ranges)
Technical simulations use cyber ranges—controlled, isolated environments that mirror production infrastructure—to execute realistic attack scenarios against defensive teams. These exercises replicate real SOC/CERT activity where analysts must detect, investigate, and respond to active threats using actual tools and playbooks.
These exercises are the closest to real SOC/CERT activity, providing the only way to validate whether security controls actually work under adversarial pressure:
- Assess SOC/CERT readiness by testing detection, investigation, and response capabilities end-to-end
- Identify tooling gaps where missing logs or capabilities hinder investigation
- Test response playbooks from alert to containment and eradication
- Evaluate team coordination including escalation and response decisions
When to Use Them
- Monthly: For regular SOC readiness validation and maintaining team proficiency through continuous practice
- Biannually or annually: As comprehensive validation of SOC capabilities and detection coverage
- After major tool deployments or architecture changes: To validate new SIEM, EDR, NDR solutions, cloud migrations, or network redesigns
Caveats
- Ensure environment fidelity: The cyber range should reflect a realistic production environment
- Consider managed platforms: Building and maintaining cyber ranges requires significant infrastructure, expertise, and ongoing operational overhead
- Avoid scenario overfitting and pattern memorization: Teams may learn to recognize specific attack patterns rather than develop generalizable investigation skills
How to Use Them Effectively
Treat simulations as controlled approximations of reality:
- Use platforms that support realistic noise injection: Legitimate user activity, false alerts, and incomplete data mimic real environments
- Leverage scenario libraries or scenario-as-a-service: Maintain variety without excessive preparation overhead by rotating attack techniques and TTPs
- Track metrics with automation: Measure reasoning, documentation, and communication using automated tracking of MTTD, MTTR, and detection coverage to build historical baselines
These exercises strengthen operational capabilities that feed into higher-level hybrid and crisis exercises.
5. Hybrid Exercises: Dynamic Tabletop with Cyber Range Simulations
Hybrid exercises combine live technical simulations with real-time injects to non-technical stakeholders, testing end-to-end coordination between technical response and business decision-making:
- Translation quality: How accurately technical findings become business decisions
- Executive pressure effects: How CEO demands impact technical performance
- Communication pipelines: Ensuring the right information reaches stakeholders at the right time
When to Use Them
- Annually: Validation of organizational crisis readiness
- After major incidents: Test updated processes and rebuild trust between teams
- When teams are siloed: Force collaboration between technical and crisis teams
Caveats
- Orchestration complexity: Requires synchronization to align SOC observations with executive briefings
- Resource constraints: Demands significant preparation, specialized platforms, and simultaneous executive availability
- Debrief complexity: Synthesizing lessons from two parallel tracks requires skilled facilitation
How to Use Them Effectively
Best for mature organizations with established detection and crisis processes:
- Synchronization tools: Automate inject delivery and ensure technical-crisis alignment
- Success metrics upfront: Define what “good coordination” looks like (time from detection to executive brief, accuracy of updates)
- Joint debrief: Debrief both teams together to identify coordination breakdowns
These exercises test “Crisis Readiness” and reveal whether your organization can survive a real breach as a unified entity.
6. Large-Scale / Systemic Exercises
Large-scale exercises simulate crises involving multiple organizations or sectors, testing ecosystem-level coordination and systemic dependencies. They reveal blind spots like vendor dependencies, shared infrastructure risks, and sector-wide vulnerabilities:
- Ecosystem coordination: How organizations collaborate during sector-wide crises
- Information-sharing: Testing ISACs, industry forums, and government partnerships
- Dependency mapping: Understanding how failures cascade across interconnected systems
When to Use Them
- Annually or biannually: For sectors with high interdependence (financial, energy, healthcare, critical infrastructure)
- Following sector incidents: Validate improved coordination mechanisms after real events
- Before regulatory deadlines: When laws require sector-wide incident response capabilities
Caveats
- Complexity and cost: Coordinating multiple organizations requires significant resources and legal agreements
- Limited technical depth: Individual teams receive less hands-on practice due to focus on coordination
- Measurement complexity: Difficult to define precise metrics and align participation across diverse organizations
How to Use Them Effectively
Require careful planning to maximize value:
- Clear objectives: Focus on 2-3 key coordination questions rather than testing everything
- Legal frameworks upfront: Ensure liability waivers, confidentiality agreements, and information-sharing protocols are in place
- Track information flow: Monitor alerts between participants, then host joint reviews to share lessons
These exercises are essential for sectors where individual resilience is insufficient and one organization’s failure can cascade into systemic collapse.
Putting It All Together: A Layered Strategy
No single exercise type provides a complete view of your cybersecurity posture. The following table provides a quick-reference summary of each exercise type, helping you select the right format for your objectives and constraints:
| Exercise Type | Target Layer | Participants | Best For |
|---|---|---|---|
| CTFs & DFIR Labs | Individual technical skills | SOC analysts, security engineers | Skill building, certification prep, onboarding |
| Tabletop | Decision-making & governance | Executives, Legal, PR, HR, IT leaders | Building crisis playbooks, aligning stakeholders |
| Dynamic Tabletop | Coordination under pressure | Crisis team, decision-makers | Testing communication, practicing escalation |
| Simulations | Operational detection & response | SOC/CERT teams, incident responders | Validating detection-to-response workflows and SOC readiness |
| Hybrid | End-to-end coordination | Technical teams + executives + stakeholders | Testing crisis readiness, bridging tech/business |
| Large-Scale | Ecosystem-level coordination | Multiple organizations, regulators, ISACs | Sector-wide threats, information sharing, systemic risks |
A mature approach involves a recurring cycle where each layer feeds into the next, moving from individual technical mastery to full organizational resilience.
From Exercises to Readiness
Cybersecurity exercises are powerful tools, but they are only as good as the intention behind them. Each format has its place; the key is understanding their limitations and combining them effectively.
Regardless of the format, the value of an exercise depends on the data it produces. Effective measurement spans both technical and organizational dimensions:
Technical & Operational Metrics:
- Detection Precision: Did we find the signal in the noise?
- Investigation Quality: Was the reasoning sound, or was it a lucky guess?
- Time Metrics: Beyond “time to detect,” track “time to escalate” and “time to inform stakeholders.”
Organizational & Business Metrics:
- Decision Quality: Were decisions based on accurate, timely information?
- Coordination Effectiveness: Did the right people collaborate without friction?
- Communication and Process Quality: Were messages consistent across audiences, and did we follow established playbooks or improvise?
Without clear metrics, exercises validate assumptions rather than capabilities.
Most organizations still test detection and crisis management in silos. Real incidents do not follow these boundaries. The ultimate goal is to build a coherent system of exercises that provides not just a plan, but a proven, measurable capability to survive.
Done right, exercises improve readiness. Done poorly, they provide something far more dangerous: a structured—but misleading—sense of confidence.
About M&NTIS Platform: For organizations seeking to operationalize this layered approach, M&NTIS is a cybersecurity training and defense testing platform designed to support both Technical/Operational Exercises and Hybrid Exercises (combining live technical simulations with dynamic tabletop injects). It provides the infrastructure to automatically run realistic live attack scenarios in isolated environments.
Reference
- ENISA Cybersecurity Exercise Methodology (February 16, 2026) - An end-to-end theoretical framework for planning, running and evaluating cybersecurity exercises. Read the publication